RFID Tags Information
RFID (radio frequency identification) tags are small electronic devices that wirelessly identify and track physical articles through radio frequency interaction with RFID readers. Each tag contains a minimum of an integrated circuit and an antenna.
RFID tags are used to label various assets with a unique electronic signature that can be encoded and read by other RFID equipment. This information is stored in non-volatile memory. Tags frequently have an Electronic Product Code (EPC), a 96-bit string of data which identifies the tag's protocol, the organization which manages the tag, asset identification, and tag serial number. Readers register the EPC of the tag and ensure its accuracy through the use of an error-correcting code algorithm. The EPC is an ambitious attempt to provide every item in the world with a unique code to track it in global databases.
Video credit: YouTube - Explania
These tags can be routinely scanned to determine the accompanying specimen's location, as well as other information such as name, ownership, transaction account, or environment. RFID tags do not need to be within the line of sight of an RFID reader. They can be placed well within the package or object as long as any RF signals remain unhindered. RFID tags can be implemented in hostile environments, and RFID readers can usually scan several hundred tags at once if supplied with anti-collision technology.
RFID tag applications are virtually limitless. Since chips can become corrupted or used to invade privacy, many RFIDs support encryption. RFID tags are also assigned an operational identity to prevent the tag from being misused.
- Read-only tags have a factory-programmed serial number which cannot be altered, and therefore cannot be misread or corrupted. A complementary internal database can be used to add supplemental information to the serial number.
- Read/write tags can have the inherited information rewritten or altered by a system user and chip reader. This information is stored in the memory of the tag chip.
- Write-once tags can be assigned an identity by a system user only once, but it can be read many times.
Active vs. Passive Tags
RFID tags contain, at minimum, two components: an antenna to collect and radiate an RF signal and an integrated circuit which stores and processes the tag identity, modulates the corresponding RF signal, and for passive chips collects power from electromagnetic waves. Passive chips rely on the ability of the antenna to perceive enough electrons from the radio frequency to charge the circuit and return its own radio frequency. Passive chips can be very small, cheap to produce, and do not need to be routinely replaced or maintained. However, the energy needed for the initial circuit charge three times the energy needed to maintain communication. Consequently, passive RFID tags have ranges of less than several feet. This characteristic can be both a design benefit (such as in credit cards) or drawback (such as in warehouse inventory).
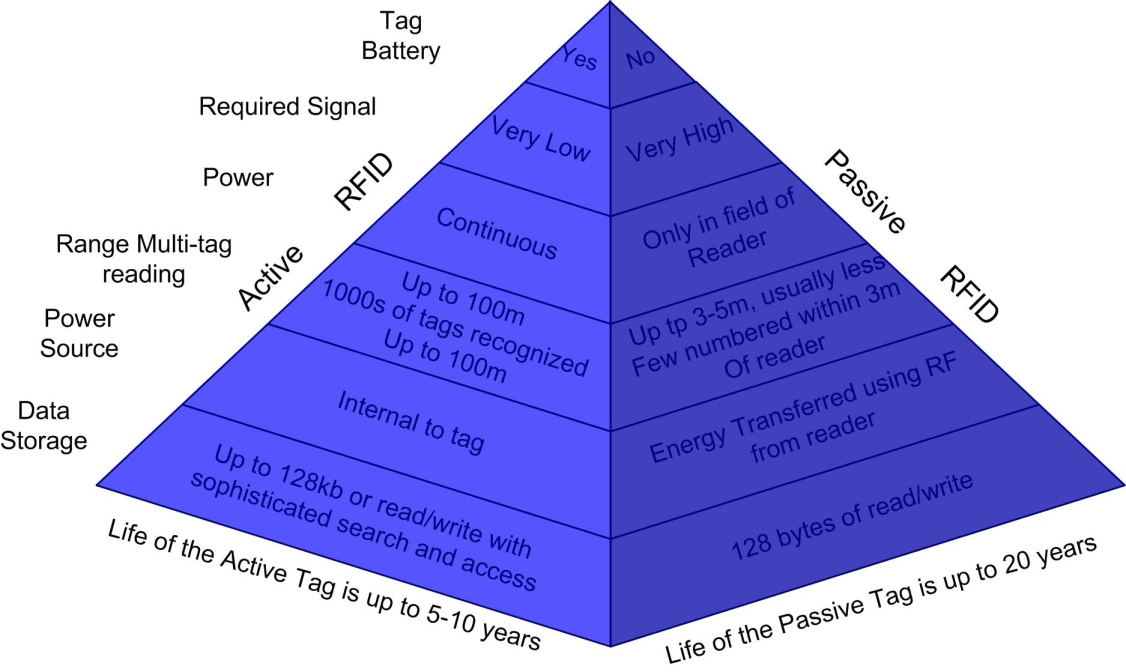
Image credit: Intech Open
Active RFIDs incorporate a battery that powers the circuit continuously. Some RFIDs transmit the ID signal periodically (active), while others wait for a reader to interrogate the tag before radiating its signal (semi-active). While an active RFID will eventually need battery replacement, the overall levels of interference and radiation are lower than in a passive RFID. Active RFIDs can also provide a range of several hundred feet.
Frequencies
The frequencies at which the reader and tag communicate are represented in the table below. Low- and high-frequency tags use the magnetic field to transfer power by induction; this signal is well-defined but rather weak. Ultra-high and microwave frequency RFID tags use the electric field for power transfer by propagation; this method has excellent range, but the reading for some tags is more ambiguous.
| Band | Range | Data speed | Common uses |
| 120—159 kHz (low frequency) | 10 cm | Low | Animal identification; factory data collection; auto keys |
| 13.56 MHz (high frequency) | 10 cm—1 m | Low to moderate | Smart cards; shelf inventories; transactions |
| 433 MHz (ultra-high frequency) | 1—100 m | Moderate | Defense applications; tracking pallets |
|
Eurasia: 865—868 MHz (ultra-high frequency) North America: 902—928 MHz (ultra-high frequency) |
1—12 m | Moderate to high | Inventory; hard-to-read RFID applications |
| 2450—6800 MHz (microwave) | 1—2 m | High | 802.11 WLAN, Bluetooth standards |
| 3.1—10 GHz (microwave) | >200 m | High | Road toll accounts |
Tag Communication
Low- and high-frequency RFID tags are usually passive or semi-active tags. These tags are less than one full wavelength away from the RFID reader and must modulate the wave produced by the reader into a return signal. This is done by oscillating the electrical load of the tag between low and high values that produces a change measurable by an RFID reader. At ultra-high and microwave frequencies, the tag is more than a full wavelength away from the reader, and with assistance from the integrated battery it can backscatter or transmit a response on a related frequency.
Image credit: Enigmatic Consulting
Tag collision occurs when an individual RFID reader perceives multiple tags simultaneously, potentially overloading the reader and making it impossible to decipher a tag's individual identity. Readers isolate tag identity in two ways. Some readers use a slotted ALOHA relay to randomly delay each tag's response, while other readers attempt to discover each RFID tag's underlying binary code by seeking random permutations from the sample set. Both systems have drawbacks, so bulk reading is not recommended for precise inventory control. Conversely, frequency hopping can be used to prevent two or more RFID readers from scanning the same chip simultaneously. This is where an RFID reader alternates between frequencies within its bandwidths to limit the chances of the same tag being interrogated twice.
Tag Implementation
RFID infrastructure is easier to operate in a closed system: a system where items tagged with RFID never change ownership. The complete history of the RFID tag is stored within an internal database which does not need to adhere to regulated RFID standards; it is also less likely to be corrupted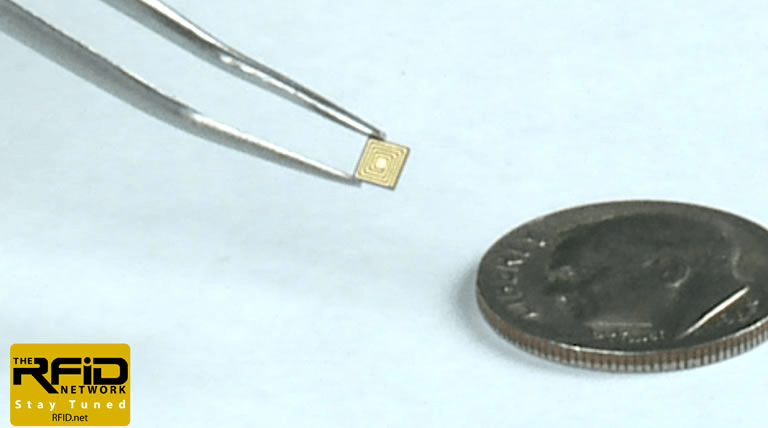
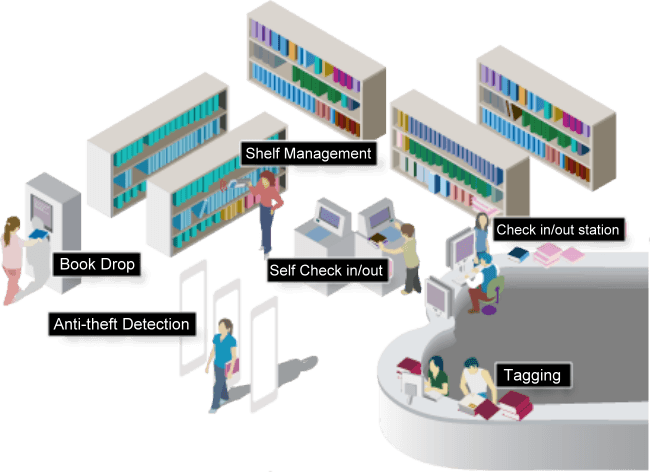
Image credits: RFID Network; RFID Library
RFID tags' small footprint is a significant reason for their current prevalence and the expected increase in their utilization. When passive tags are employed correctly they can be nearly impossible to recognize visually. The smallest RFID tags ever created were passive tags affixed to ants to study colony behavior. They are often incorporated into merchandise in a process known as electronic article surveillance, where the RFID tag must be overwritten at the point-of- purchase to prevent an alarm at the store exit from sounding. Even active tags, which must include a battery, are usually no larger than a matchbook and are used in many shipping and cargo applications. Furthermore, RFID tags are exceptionally cheap, with most passive tags costing less than $1 USD each, and active tags costing just a few times more, where the initial expense is usually worth the investment.
NFC (Near Field Communication)
NFC, or near field communication, is a short range subset of radio-frequency identification (RFID) communication protocols that use electromagnetic radio fields for connecting electronic devices. NFC enabled devices maybe passive or active with passive devices allowing only reading from other devices while active can read and send information. NFC operates at 13.56 MHz at a distance of 4 cm and has a data transfer rate up to 424 kbps. It is used in the consumer electronics industry allowing users to connect to other NFC enabled devices without compromising personal data.
Standards
Since each country may allocate different frequencies for RFID, the bands utilized are different around the world. As such, RFID tagging is rarely compatible with international equipment, and local and regional legislation may apply when utilizing RFID. The industrial standards in the list below are widely accepted.
- ISO 14223 RFID use on animals
- ISO 14443 RFID use in passports and ID cards
- ISO 15693 RFID use for financial transactions
- ISO 18000 RFID use for item management
- ASTM D7435 Performance of passive RFID tags in loaded containers
RFID Tag Applications
It would be impossible to name every application in which RFID is useful. The following examples provide a good representation of the capabilities of RFID tags.
RFID tags can used as payment alternatives. Tags can be linked to credit or bank accounts and can be scanned by an RFID reader. The transaction is complete once the owner enters a private, preset PIN. These types of tags are common in cell phones, key chains, poker chips, and within credit cards themselves.
Factories, warehouses, cargo operations, and delivery services regularly implement RFID tags for asset tracking to distribute and track cargo accurately and instantaneously. Large businesses and corporations may also tag important information technology devices and electronics for quick locating. Manufacturers may keep track of assets far along the supply chain to analyze efficiency. 
Tags are regularly incorporated in merchandise to help retailers maintain an accurate inventory and speed up the locating of particular items. There is speculation that RFID chips may one day replace bar codes, since hundreds of tags can read read at once.
ID badges and electronic keys frequently incorporate RFID tags. This allows selective access to locked doors and restricted areas without the need to exchange or keep track of mechanical keys.
RFID tags are occasionally affixed to humans. It is a common practice on oil rigs to tag important personnel so they can be found quickly in the event of an emergency.
Within passports, RFID tags allow the passport to be read digitally and the individual is assessed against a database to determine entry eligibility.
RFID tags are frequently placed in cars so drivers do not have to come to a stop to pay a toll. Similar measures have been used for buses and trains.
Animal identification is a common usage of RFID tags. They are used to identify livestock, as well as assist in locating of missing pets.
Hospitals have considering using tags to offer an immediate electronic history of the patient without the need for an accompanying physical record.
Many races (foot, automotive, and others) use tags to provide an exact readout of race times.
Resources
Wikipedia - Radio-frequency identification
Image credits:
Explania | Intech Open | Enigmatic Consulting | RFID Network | RFID Library | Easi-Card
